Not all clouds are created equal, at least not in terms of security.
Companies switching cloud services or adopting cloud services must be fully aware of the capabilities and risks of every cloud services software available to them.
Multicloud environments are incredibly popular today; according to a survey conducted by IBM, 85% of companies use multicloud environments. The same survey revealed 98% of companies plan to adopt multiple hybrid clouds by 2021.
While multicloud environments are elastic and customizable, multicloud requires additional scrutiny and dedicated management. Companies must configure and integrate various cloud services properly to avoid attacks, data leaks, and security breaches.

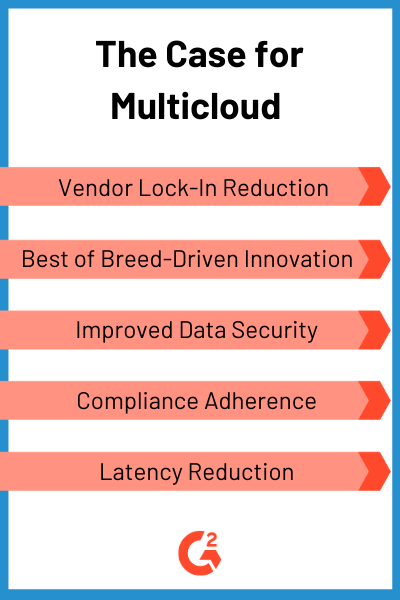
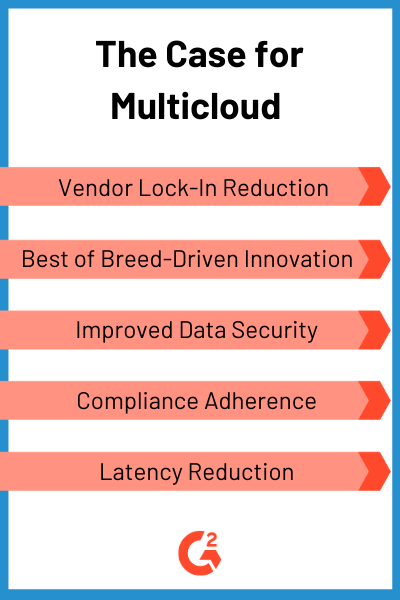
There’s good reason so many companies are considering multicloud solutions, most obviously, to avoid putting all their eggs in one basket. In other words, companies are looking to multicloud to boost their overall efficiency and cut spending. That holds true for the most part; however, a properly secured multicloud environment requires additional effort and technology.
While nearly half (48%) of corporate data is stored in the cloud, only 32% of organizations admit they employ a security-first approach to data storage in the cloud, according to a report from the Thales Group.
This is concerning.
Companies must prioritize security above everything for the sake of their business and their customers. Without it, cloud services open businesses up to unlimited threats that can result in data loss, steep fines, or theft of proprietary information.
Multicloud vs. other cloud environments
Before we dive in to the challenges associated with multicloud environments, let’s differentiate multicloud systems from other common cloud services.
Public cloud — The public cloud is utilized through cloud service providers like AWS, Microsoft Azure, or Google Cloud. These various services run on the provider’s infrastructure and typically use a pay-per-use model. They eliminate the need for businesses to manage infrastructure and shared resources.
Private cloud — Private clouds are the simplest cloud environments one can imagine, operating within a company’s own network. Private clouds require localized infrastructure and management. Many cloud services providers offer virtual private clouds, which are isolated, virtualized cloud environments running on public cloud infrastructure.
Hybrid cloud — Hybrid cloud environments combine aspects of public and private cloud environments. Businesses typically utilize public cloud resources for major operations, but store sensitive data on local, private infrastructure. Hybrid clouds can be some of the most flexible solutions, but can also be some of the most difficult to manage.
Multicloud — Multicloud environments utilize multiple cloud environments for specific tasks and operations. Unlike hybrid cloud environments, multicloud environments might use multiple public or private clouds, or a combination of the two. These individual clouds typically operate independently. For example, a multicloud environment might run all computing activities from one cloud service provider, databases from another service provider, and utilize local infrastructure to store sensitive data.
Common issues with multicloud security
While multicloud environments provide a myriad of benefits, there are numerous threats and issues that may arise as a result of multicloud adoption.
Access control — One of the simplest ways for someone to obtain sensitive information is by misusing permissions granted by an administrator. Social engineering makes stealing credentials as easy as sending a phishing email. Proper network access control management across multiple cloud environments requires continuous monitoring of permissions and user behavior. Companies must ensure only approved parties interact with sensitive data while certifying no data is moved from a secure location to a vulnerable environment.
Authentication — Even with access control and identity management, companies should still enforce multiple layers of authentication on every cloud service that stores sensitive data. The easiest way to do this is utilizing multi-factor authentication (MFA) tools that require secondary verification via SMS code, key generator, or email. Additionally, risk-based solutions take multiple risk factors such as location, behavior, or permissions into account. These types of software are becoming more common as they consider numerous variables to mitigate risk.
Compliance — With multiple cloud environments interacting with business information, it can be difficult to ensure every piece of sensitive data is properly labeled and secured. Various municipalities have specific regulations that pertain to data privacy and security compliance. A company must ensure the information they store is compliant in every location they conduct business.
Vulnerability management — Applications and networks require frequent testing and scanning for vulnerabilities. Otherwise, firewalls or other security mechanisms could be easily bypassed with something as simple as SQL injection. In addition to traditional vulnerability scanners, companies should utilize threat intelligence software to ensure their cloud resources are protected from the most advanced threats on the internet.
Best practices for multicloud security systems
Centralized visibility — Multicloud environments have numerous moving parts and siloed systems. This makes it difficult for businesses to paint a full picture of every cloud service they use, how they are connected, and who has access to them. Numerous tools have been introduced in recent years that enable companies to gain visibility into their multicloud environments. Cloud management platforms are the easiest way for companies to centralize control of various clouds and enforce compliance across multicloud environments.
Workload protection — Workloads are the functions and resources that run in a cloud environment. In a multicloud scenario, these often operate independently and require individual attention. Cloud workload protection platforms help ensure each individual workload is properly configured and vulnerabilities are accounted for. They also assist in behavior monitoring to detect misuse and intrusions.
“Beam is a very good tool for Multicloud optimization that provides organizations with deep visibility and rich analytics detailing cloud consumption patterns, along with one-click cost optimization across their cloud environments. It has Centralized management and optimization of customers complete compute infrastructure, Cost visibility and cost tracking.”
— Nutanix Beam Review
Data governance — Because 21% of files in the cloud contain sensitive data, it’s incredibly important to maintain continuous visibility of datastores. If you don’t use them already, consider data-centric security solutions to simplify the discovery and tagging of sensitive information. Cloud compliance software can also help manage security and compliance policies across cloud workloads.
Policy enforcement — Policy enforcement and configuration management are some of the most difficult tasks associated with managing a multicloud environment. These policies include a combination of security measures to facilitate access control, protect environments, secure sensitive data, and prevent misuse. Each security mechanism that protects various cloud environments requires specific configurations for its individual cloud service and use case. Misconfigurations can expand the likelihood of an attack; furthermore, poor security policies and misconfigurations open up cloud environments to a plethora of threats.
"Companies can meet their complex security needs in both their old and new environments, while providing user-friendly end user authentication."
— Merry Marwig, market research analyst - privacy & security, G2

Recent news in multicloud security
The majority of businesses either currently utilize or plan to adopt a multicloud solution in the near future. As a result, the multicloud security and management market is growing; venture funding and major acquisitions are evidence of the markets huge expansion.
Earlier this year Google announced the release of Anthos, a tool designed to build and manage applications in hybrid and multicloud environments. Anthos can be used to build, manage, and deploy applications on the Google Cloud Platform (GCP) with Google Kubernetes Engine (GKE).
| Related: Read more about emerging trends in AI, analytics, the cloud, and data privacy from G2 analysts specializing in technology research. |
This tool is can be used to automate enterprise security protocol and other policies across multicloud environments. This can help manage and enforce strict role-based access controls while monitoring behaviors, traffic, and performance across complex IT systems.
This October, Aviatrix received $40 million in Series C funding from CRV. Aviatrix provides networking and security services for the multicloud enterprise. The “service” is delivered through a number of modular, virtualized components. The centralized management platform provides full network visibility and control. Users can automate complex networking tasks, monitor clouds across multiple accounts, and deploy virtualized security tools to manage domains, connections, firewalls, and policy events.
Also in October, Fortinet purchased the security vendor enSilo for an undisclosed amount, but, before the acquisition, enSilo had raised upward of $50 million in funding. Fortinet plans to expand the functionality of its FortiSIEM, FortiInsight, and FortiNAC offerings. Fortinet says the expanded functionality will allow greater visibility and coordinated control of networks, users, and activities from endpoints to multicloud environments.
Aside from mergers, acquisitions, and venture funding, established security vendors like FireEye expanded functionality to adapt to multicloud environments. Earlier this month, FireEye announced new functionality for its helix security platform that’s specifically designed to improve the security of multicloud environments. The company released a statement about the change.
“Too often, organizations lack the necessary controls and expertise to extend their visibility and protection across complex multi-cloud infrastructures. These releases extend the power of FireEye technology and intelligence through a cloud-based architecture for scalable detection, centralized visibility, configuration monitoring, and user behavior analytics. Working seamlessly, these capabilities empower organizations to identify advanced attacks that bypass traditional defenses.”
— Excerpt from Fortinet statement
Looking to the future, more companies will consolidate and virtualize their existing tools, and offer a centralized platform for multicloud security. These tools will improve control and increase security for cloud environments while automating tasks such as monitoring, detection, and remediation.
Companies must consider various cloud management platforms and cloud security solutions available to improve their network visibility and bolster their cloud security.