Why We Are Merging the DDoS Protection and Cloud DDoS Mitigation Categories
From time immemorial, humans always had to find ways to deal with their fellow troublemakers.
 by Amal Joby
by Amal Joby
Navigating Buyer Preferences for Biometric Authentication Software
G2 is the place you go for software, and it’s also the place where software buyers return to leave...
 by Brandon Summers-Miller
by Brandon Summers-Miller
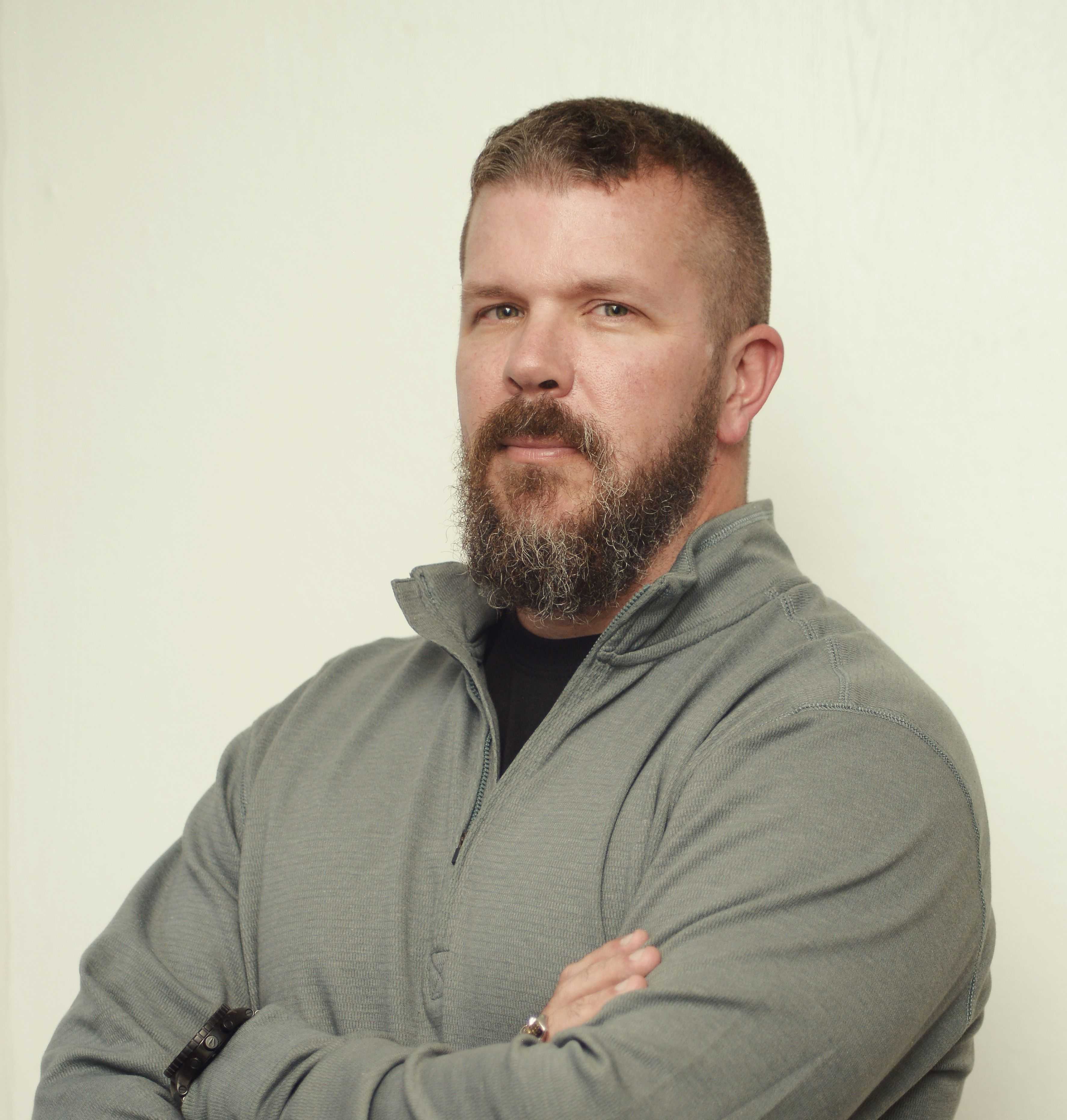
The Hard Truth: Why Cyber Insurance Companies Should Demand Valid & Tested Cybersecurity Plans
In today's digital age, the importance of cybersecurity cannot be overstated.
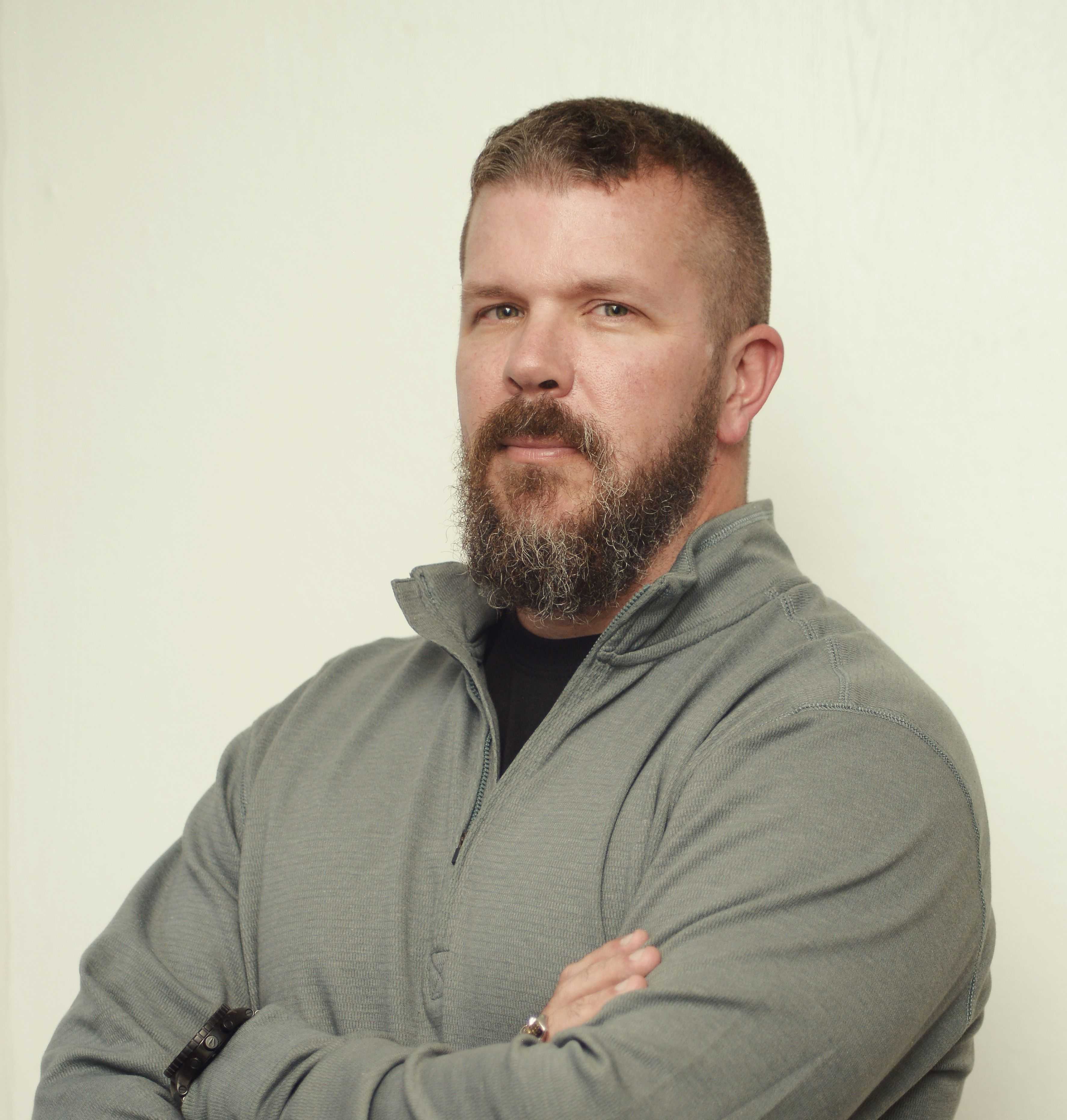 by Dr. Chase Cunningham
by Dr. Chase Cunningham
Ending the Zero Trust, SSE, and SASE Confusion
Zero Trust, Secure Service Edge (SSE), or Secure Access Service Edge (SASE) are related concepts in...
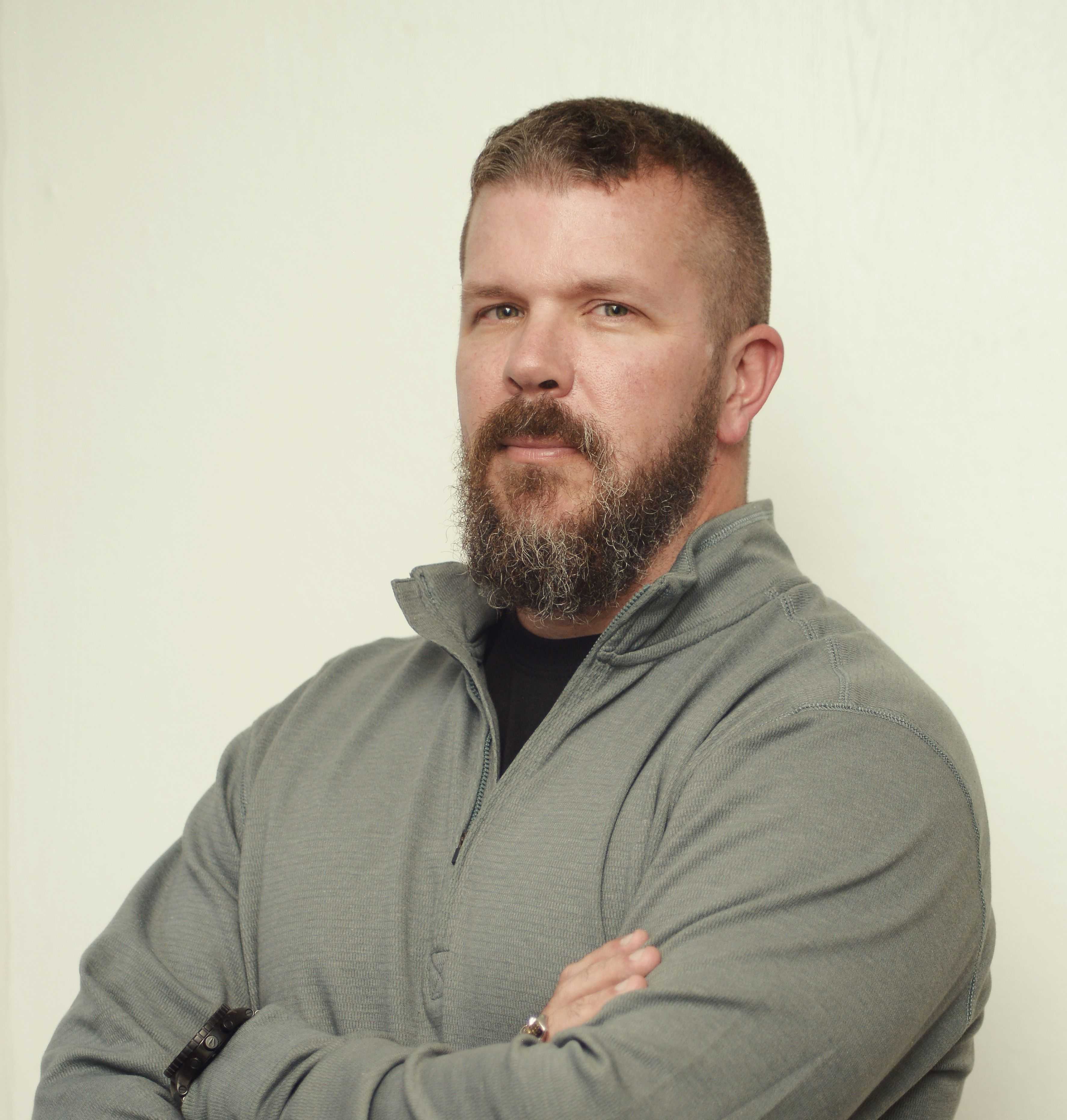 by Dr. Chase Cunningham
by Dr. Chase Cunningham
Data Security Has Evolved beyond DLP; Don’t Let Those Scars Hinder Your Security Strategy
Data loss prevention (DLP) security has significantly changed over the last few years. These...
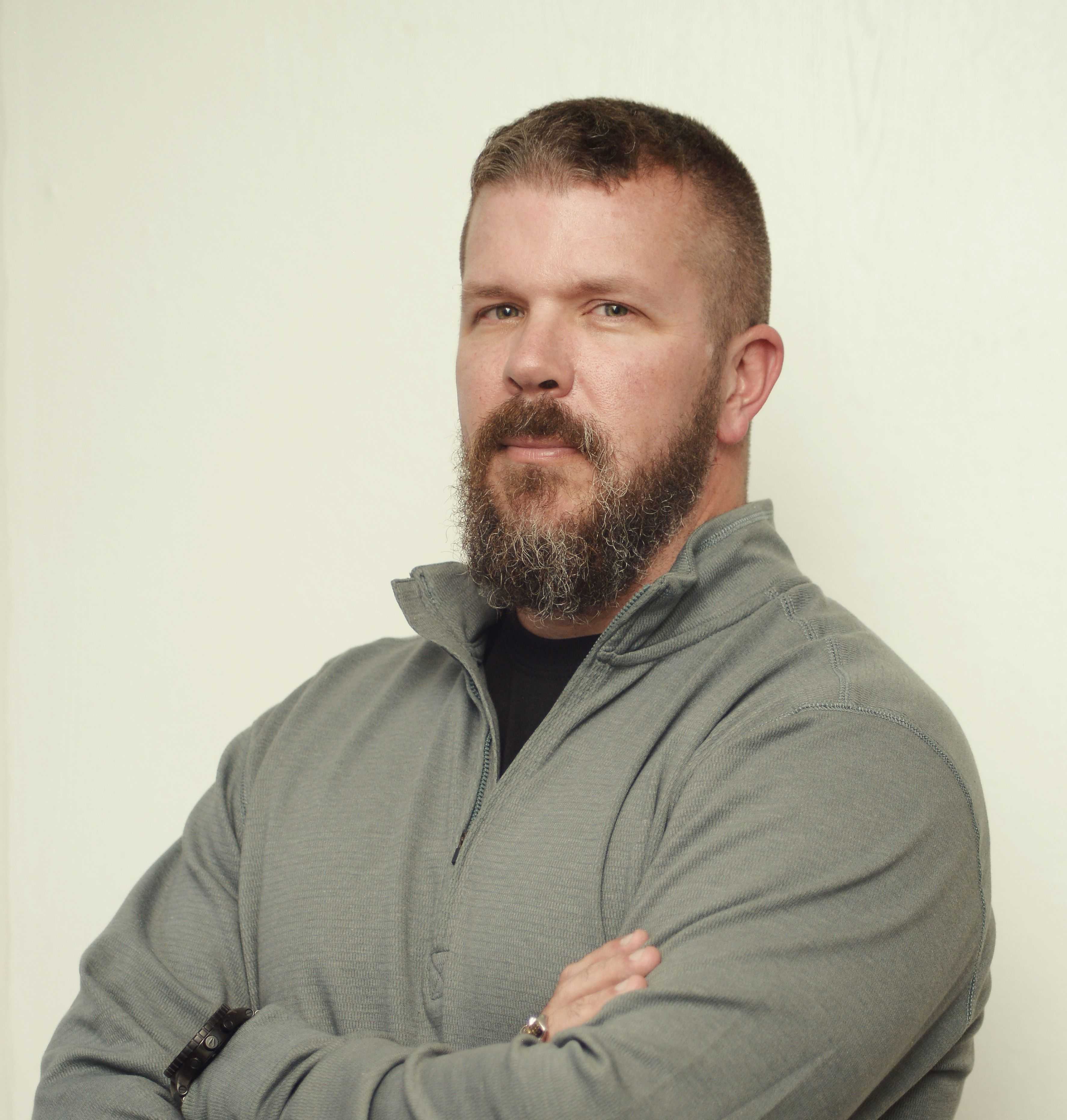 by Dr. Chase Cunningham
by Dr. Chase Cunningham
2024 Trends: Projections and Preparedness in Cybersecurity
This post is part ofG2's 2024 technology trendsseries. Read more about G2’s perspective on...
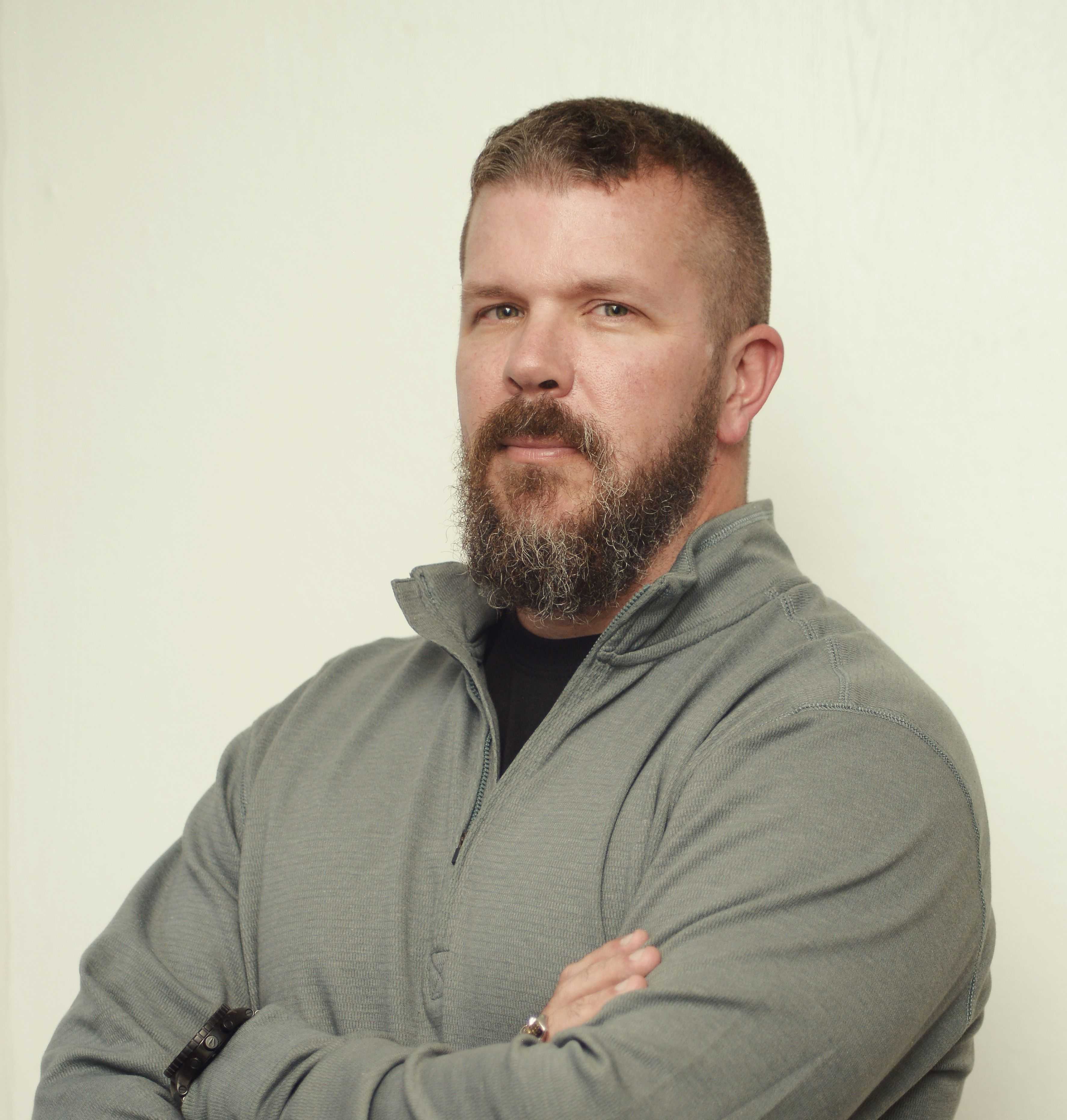 by Dr. Chase Cunningham
by Dr. Chase Cunningham
Shiny Object Syndrome With Value Discipline
Shiny object syndrome is a term used to describe a behavioral pattern where individuals easily get...
 by Dr. Chase Cunningham
by Dr. Chase Cunningham
2023 Trends in Cybersecurity: Proactive Security Becomes De Facto
This post is part of G2's 2023 digital trends series. Read more about G2’s perspective on digital...
 by Amal Joby
by Amal Joby
2023 Trends in the Secure Access Service Edge (SASE) Market
This post is part of G2's 2023 digital trends series. Read more about G2’s perspective on digital...

.png?height=458&name=Light%20(7).png)
.png?height=458&name=Light%20(5).png)


%20Will%20Grow%20in%202023.png?height=458&name=Investments%20in%20Secure%20Access%20Service%20Edge%20(SASE)%20Will%20Grow%20in%202023.png)
